PHP Code Quality Checklist for Safer Releases

Most PHP release failures are not “mysterious production bugs”. They are predictable outcomes of weak guardrails: inconsistent code style, missing types, risky refactors without tests, unreviewed dependency changes, and last-minute deployment surprises.
A good PHP code quality checklist turns those risks into automated evidence. The goal is not perfection, it is repeatable, safer releases where the team can answer, “what changed, what could break, and how would we know?”
Below is a pragmatic checklist you can apply to Symfony, Laravel, or custom PHP codebases, including legacy systems where you cannot fix everything at once.
How to use this checklist (so it actually ships)
Treat items as quality gates (must pass), quality signals (tracked but not blocking), and hardening work (planned improvements). For most teams:
- Quality gates run on every pull request.
- Quality signals run on main nightly (or on demand).
- Hardening work becomes explicit backlog items tied to hotspots.
If you already have an established delivery system, map these checks into it. If not, start by adding two gates (formatting and static analysis) and expand.
PHP code quality checklist (the practical version)
1) Establish a clear runtime and repo baseline
Before you talk about “quality”, make the execution context explicit.
Your baseline should answer:
- Which PHP version(s) are supported (and enforced in CI)?
- Which extensions are required (intl, gd, redis, etc.)?
- Is
composer.lockcommitted (it should be for applications)? - Is autoloading PSR-4 consistent, and are namespaces aligned with folders?
This prevents “works on my machine” and makes every other check meaningful.
Quality gate suggestion: CI uses the same PHP version as production (or a matrix if you support multiple runtimes).
2) Enforce formatting and coding standards
Formatting is not just aesthetics, it reduces review noise and makes risky diffs easier to spot.
Common, proven defaults:
- Adopt PSR-12 for baseline style.
- Use one formatter and run it automatically.
Tools used widely in PHP:
- PHP CS Fixer for automatic fixing.
- PHP_CodeSniffer if you want sniff-based enforcement.
Quality gate suggestion: formatting check must pass on PR, and the team agrees on one tool so developers do not fight the robot.
3) Add static analysis as a “release safety net”
Static analysis is one of the highest ROI safeguards in modern PHP, especially since PHP 8+ introduced stronger typing capabilities.
Two common choices:
What static analysis catches that reviews often miss:
- Calling methods on possibly-null values.
- Returning the wrong type (especially in service boundaries).
- Wrong array shapes (a frequent source of runtime notices in legacy code).
- Dead code and unreachable branches.
Legacy-friendly approach: start with a baseline file and focus on new and changed code. Most teams fail here by trying to “fix all findings” upfront, then giving up.
Quality gate suggestion: no new static analysis issues introduced in changed files, and a steady plan to ratchet the level upward.
4) Make type intent explicit where it matters
Not every PHP codebase can be “fully typed”, but releases become safer when type intent is consistent on boundaries.
High-leverage places to tighten types:
- Public methods on services used across the application.
- DTOs and request/response models.
- Event payloads and message handlers.
- Persistence boundaries (repositories), especially where arrays are returned.
Practical PHP habits that reduce production surprises:
declare(strict_types=1);in new files (and incrementally elsewhere if feasible).- Prefer named constructors and value objects for critical domains.
- Use PHPDoc for array shapes when you cannot model a type yet (then let static analysis enforce it).
Quality signal suggestion: track the number of suppressed issues or baseline size and require justification for new suppressions.
5) Keep tests aligned with release risk, not ideology
A “good test suite” is not defined by coverage percentage alone. It is defined by how well it reduces change failure rate.
Common, effective layers for PHP apps:
- Unit tests for pure logic.
- Integration tests around database queries, external service adapters, queues.
- HTTP-level tests for core user workflows (even a small set is valuable).
Mainstream tooling:
What to enforce for safer releases:
- Tests run in CI on every PR.
- Flaky tests are treated as incidents (they destroy trust in the safety net).
- Critical bug fixes ship with a regression test, unless you explicitly document why not.
Quality gate suggestion: tests must pass, and the suite finishes within a time budget that keeps feedback loops tight.
6) Prevent “dependency drift” and supply chain surprises
Many PHP production incidents are not caused by your code, they are caused by dependency changes landing silently.
Checklist items that reduce this risk:
- Commit
composer.lock. - Keep dependencies current enough that security patches do not require heroic upgrades.
- Ensure abandoned packages are identified and replaced.
Use Composer’s built-in security checks:
- Run
composer auditin CI.
Quality gate suggestion: fail PRs that introduce new high severity vulnerabilities, and set a timeboxed policy for fixing existing ones.
7) Add security checks that match real PHP failure modes
Code quality and security overlap heavily. A secure release is often the result of disciplined boundaries.
Practical checks for PHP projects:
- Secret scanning on commits and PRs (tokens, private keys).
- Basic SAST on pull requests.
- A dependency vulnerability gate (covered above).
- Input validation and output encoding conventions.
If you need an industry reference to shape “what good looks like”, OWASP ASVS is a solid checklist-style standard that maps well to web apps.
Quality signal suggestion: track vulnerability age (how long known vulnerabilities remain unfixed), not just counts.
8) Guard your database changes like production code
In PHP applications, database changes are often the true release risk.
Release-safety checks:
- Migrations are reversible where possible, or explicitly marked as non-reversible.
- Long-running migrations are planned (batching, background backfills, feature flags).
- Queries added in the release are reviewed for N+1 patterns and missing indexes.
If your app uses an ORM (Doctrine, Eloquent), add checks that focus on behavior, not framework purity. For example, review high-traffic endpoints for query count, transaction scope, and lock risk.
Quality gate suggestion: migrations run successfully in CI against an ephemeral database, and your deployment process is compatible with zero-downtime patterns.
9) Require “production evidence” for performance and reliability
A safe release is not only about correctness, it is also about not degrading latency, error rates, and resource consumption.
Practical checklist items:
- Key endpoints and background jobs have timeouts and predictable retry behavior.
- Error handling is intentional, not “catch everything and ignore”.
- Logging includes enough context to debug (request id, user/tenant id, correlation id).
Even without a full performance program, you can enforce:
- A small set of smoke tests on staging.
- A rollback plan (or a forward-fix plan) that is realistic.
Wolf-Tech’s broader delivery guides cover these release-safety mechanics in detail, for example the CI/CD foundations in CI CD Technology: Build, Test, Deploy Faster.
10) Make code review effective (and measurable)
Code review is part of code quality, but only if it has clear standards.
Review is strongest when it focuses on:
- Risky changes in hotspots, not bikeshedding.
- Boundary correctness (API contracts, data models, authorization).
- Failure modes (timeouts, nullability, retries, idempotency where relevant).
A lightweight rule that improves outcomes fast: keep PRs small enough that reviewers can actually understand them. If you want to tie this to metrics, Wolf-Tech’s article Code Quality Metrics That Matter explains how to measure review flow without gaming.
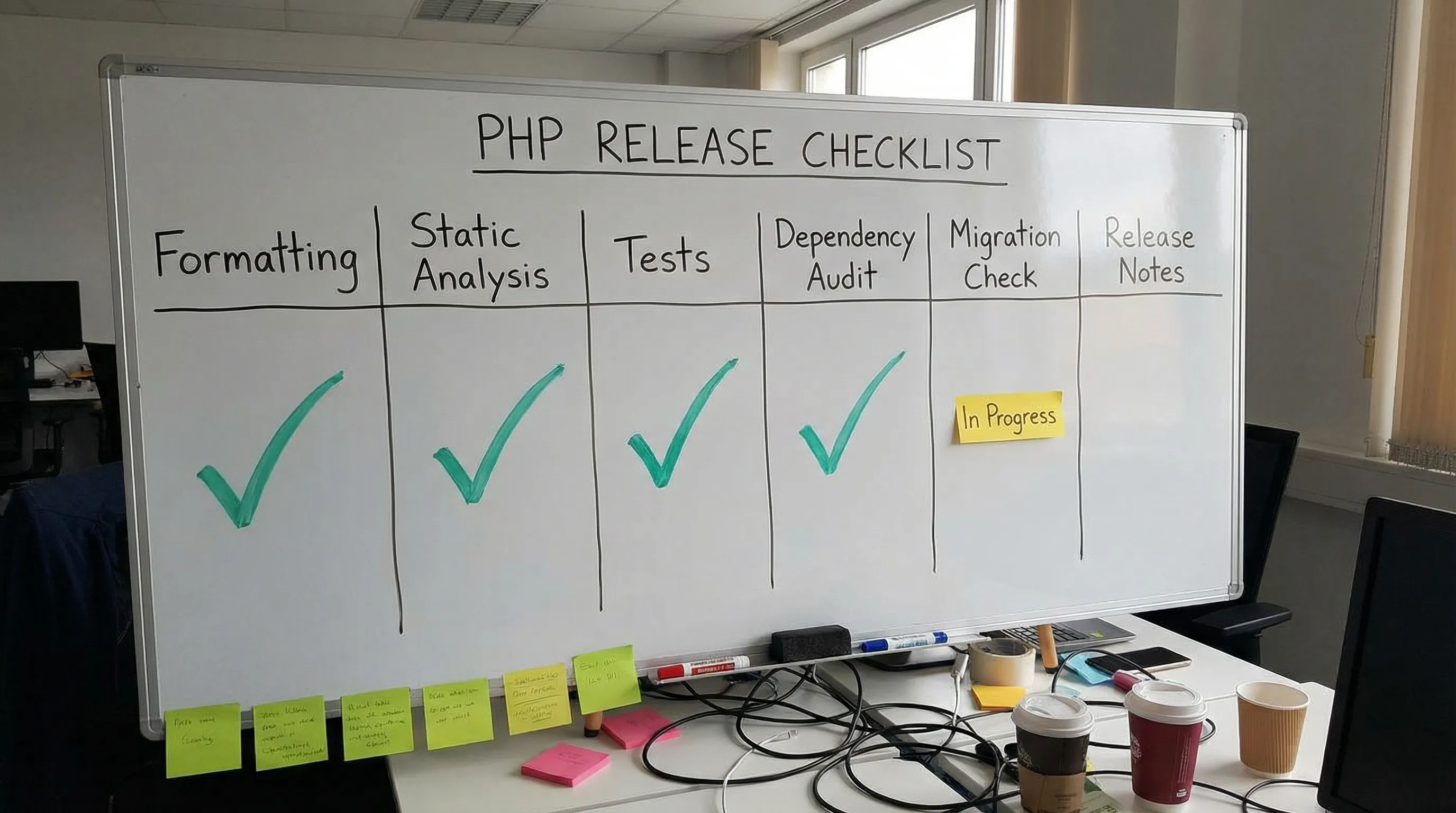
A compact “gate vs signal” table you can copy into your repo
Use this as a starting point for your CONTRIBUTING.md or engineering handbook.
| Area | What to check | Common tool choices | Recommended stance |
|---|---|---|---|
| Formatting | PSR-12 style, consistent imports | PHP CS Fixer, PHPCS | Gate on PR |
| Static analysis | Type errors, nullability, dead code | PHPStan or Psalm | Gate on PR for changed code, baseline for legacy |
| Tests | Unit + integration + minimal workflow tests | PHPUnit, Pest | Gate on PR |
| Dependencies | Known vulnerabilities, abandoned packages | composer audit | Gate on PR for new high severity issues |
| Secrets | Credentials in commits | Secret scanning (CI provider or git hooks) | Gate on PR |
| DB migrations | Migrations apply cleanly, rollout compatible | Framework tooling + ephemeral DB | Gate on PR where applicable |
| Reliability basics | Timeouts, retries, error handling patterns | Review + targeted tests | Signal initially, then gate on critical paths |
| Observability | Meaningful logs, error reporting configured | Logging + APM/Sentry style tools | Signal, then gate for core services |
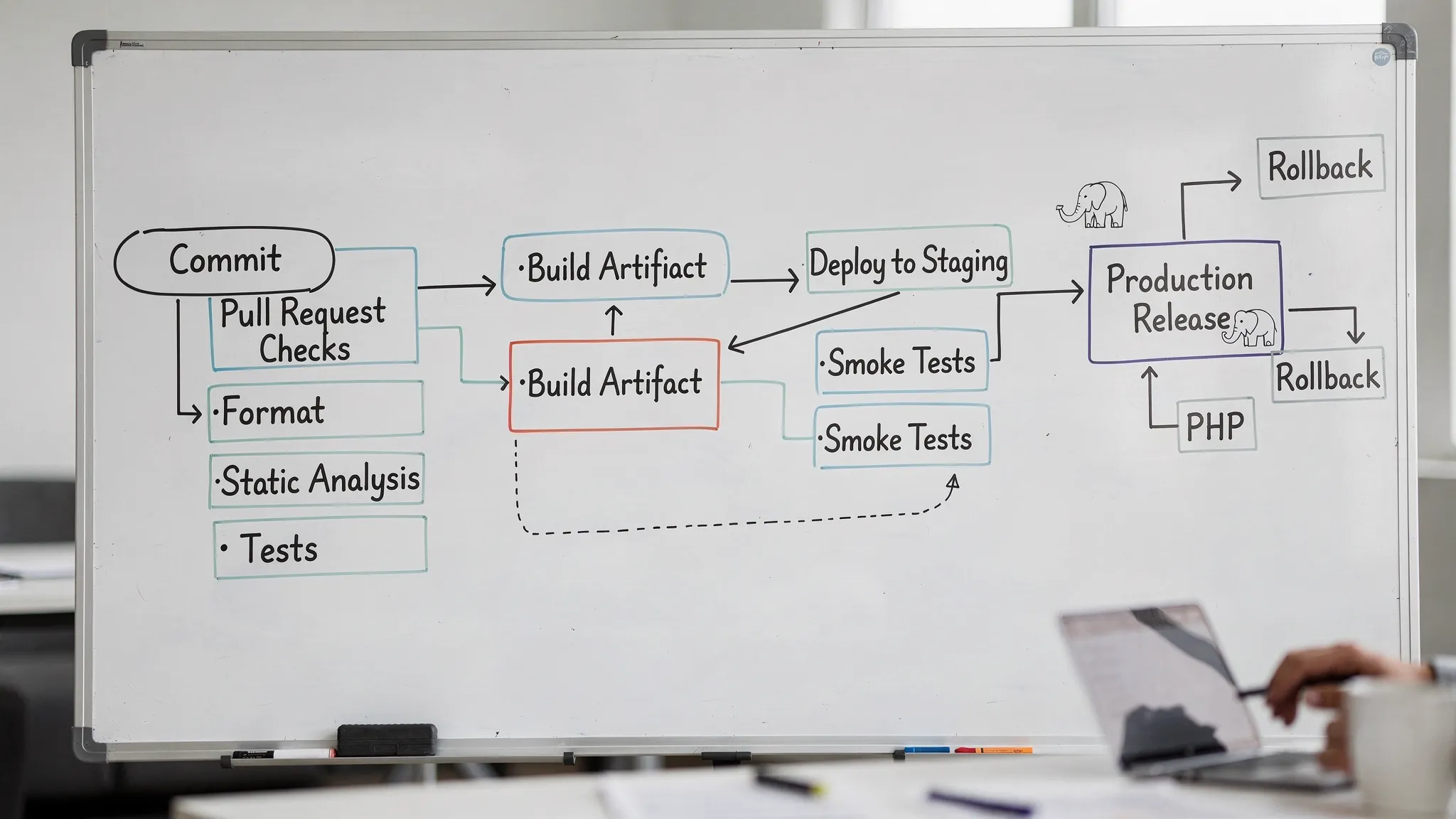
Minimal CI recipe (vendor-neutral)
Your CI should run the same core stages every time, regardless of whether you use GitHub Actions, GitLab CI, CircleCI, or something else.
A common set of PR checks for PHP:
- Install dependencies (use cache, but ensure correctness).
- Lint and format check.
- Static analysis.
- Test suite.
- Security audit for dependencies.
Example command set (adapt to your tools):
composer install --no-interaction --prefer-dist
composer lint
composer format:check
composer stan
composer test
composer audit
If your repo does not have these scripts yet, add them. Making checks callable via Composer scripts keeps onboarding simple and prevents “CI-only knowledge”.
Rolling this out in a legacy PHP codebase (without stalling delivery)
Legacy projects rarely fail because they lack a perfect target state. They fail because the path to improve quality is unrealistic.
A rollout strategy that tends to work:
- Start with formatting, because it is low risk and reduces review friction.
- Add static analysis with a baseline, then enforce “no new issues in changed code”.
- Add “diff coverage” expectations for risky modules rather than chasing global coverage.
- Use refactoring only when you can lock behavior with tests, especially in hotspots.
This aligns well with the incremental modernization approach described in Refactoring Legacy Applications: A Strategic Guide.
What “safer release” should look like in practice
When this checklist is implemented well, you should see measurable outcomes:
- Fewer production incidents caused by null/type issues, missing branches, or refactor regressions.
- Faster reviews (less noise, smaller PRs, clearer intent).
- Reduced change failure rate and faster recovery, because releases are more observable and reversible.
If you are already tracking delivery metrics, you can connect the dots directly. If not, start with a simple weekly scorecard and iterate.
When to bring in outside help
If your PHP codebase is revenue-critical, highly regulated, or simply too risky to change, a checklist alone is not enough. You typically need:
- A short code quality audit (tooling, hotspots, dependency risk).
- A CI quality gate design that matches your release process.
- A staged remediation plan that preserves delivery.
Wolf-Tech provides full-stack development and code quality consulting for teams modernizing and scaling PHP systems. If you want a second set of eyes on your quality gates or a practical rollout plan, you can reach out at wolf-tech.io.

