Software Systems 101: Boundaries, Contracts, and Ownership

Most software systems don’t fail because the team chose “the wrong framework.” They fail because the system’s boundaries are fuzzy, its contracts are implied, and ownership is unclear. That combination produces the classic symptoms: duplicated logic, surprise breakages, “who owns this?” incidents, and roadmap paralysis.
Think of this as a 101-level primer that gives you a practical mental model you can apply to legacy monoliths, modular monoliths, microservices, data platforms, and even UI-heavy web applications.
What a “software system” really is
A software system is not just code. It is a socio-technical bundle:
- Executable components (services, jobs, apps, libraries)
- Data stores and data flows
- Interfaces (APIs, events, files, UI contracts)
- Operational reality (deployments, alerts, incident response)
- People and decision rights (teams, ownership, governance)
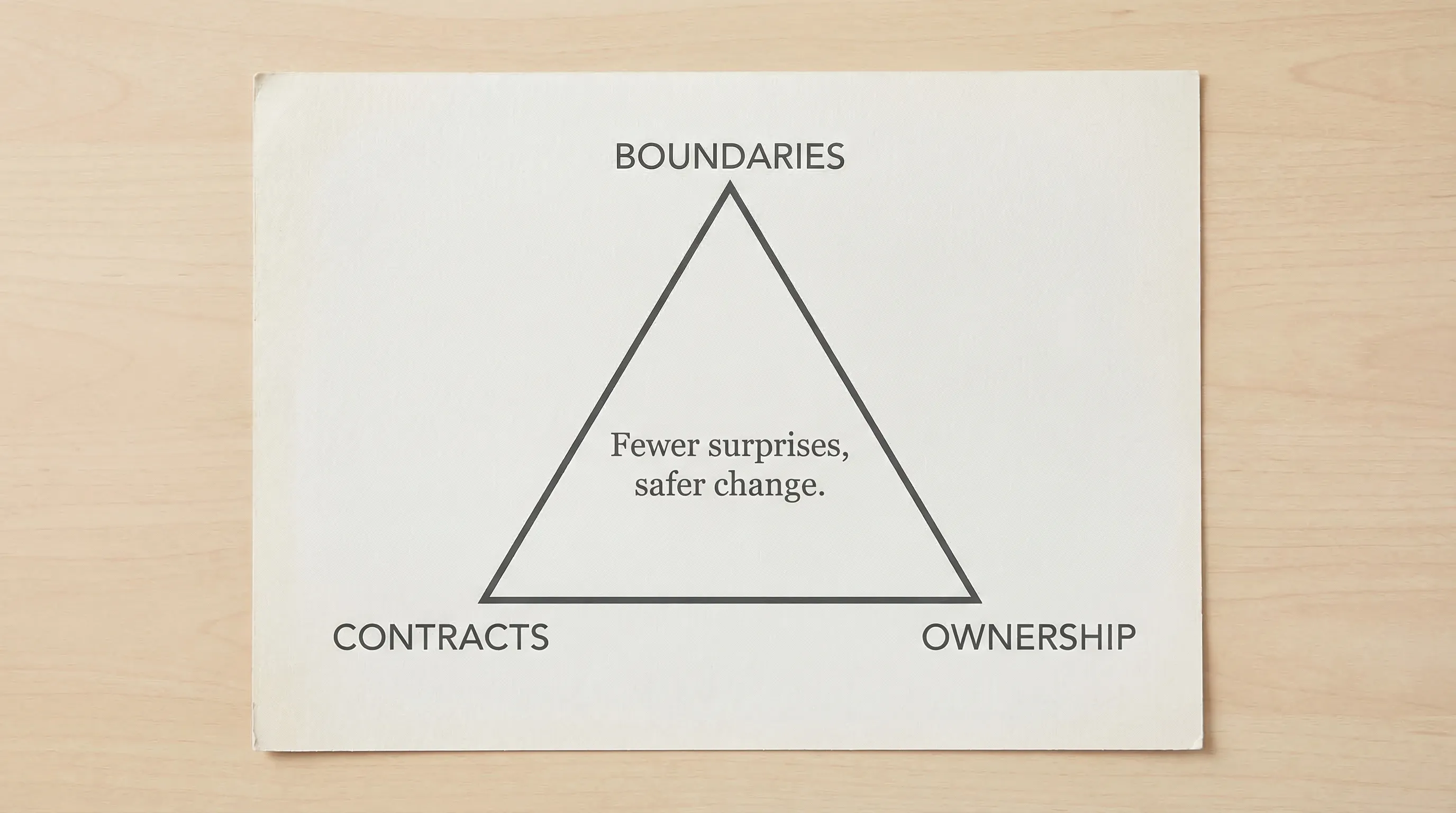
When leaders say “we need better architecture,” they often mean “we need fewer surprises.” Fewer surprises come from making three things explicit: boundaries, contracts, and ownership.
Boundaries: where responsibilities stop
A boundary is the line that answers: “What is inside this thing, and what is outside?” Good boundaries reduce coordination cost and prevent changes from rippling everywhere.
Common boundary types in software systems
| Boundary type | What it separates | Good default signal | Common failure mode |
|---|---|---|---|
| Code/module boundary | Packages, modules, libraries | Different reasons to change | “Shared utils” becomes a dumping ground |
| Service/runtime boundary | Deployable units (APIs, workers) | Independent scaling or isolation needs | Microservices created for org politics, not constraints |
| Data boundary | Databases, schemas, ownership of tables | One source of truth per domain | Many services writing the same tables |
| Integration boundary | Third-party systems, partner APIs | Different trust and failure domains | Tight coupling to vendor quirks and outages |
| UX boundary | Frontend modules, BFFs, page areas | Different user journeys and states | UI depends on too many backends directly |
How to draw boundaries that last
A practical way to start is to align boundaries to business capabilities (often described as “bounded contexts” in Domain-Driven Design). You don’t need to adopt full DDD to benefit from the core idea: group what changes together, separate what changes for different reasons.
High-signal heuristics:
- Change cadence: If two areas ship at different speeds, force a boundary.
- Risk profile: Payments, identity, and compliance-heavy logic often deserve isolation.
- Data lifecycle: If data has different retention, auditing, or privacy rules, separate its ownership.
- Operational blast radius: If failures must not spread, isolate dependencies and deployables.
What to avoid:
- Boundaries based on org chart alone (those change faster than domain realities).
- “One team per microservice” when you do not yet have platform maturity.
- Shared databases across many services without strict write ownership.
If you are early in a product’s life, a modular monolith often gives you most boundary benefits without distributed-system overhead. (Wolf-Tech has a deeper guide on that pattern if you want to go further: Software Applications: When to Go Modular Monolith First.)
Contracts: how parts of the system promise to behave
Once you have boundaries, you need contracts across them. A contract is a testable promise that lets teams change internals without breaking consumers.
In practice, contracts are more than API docs. They include:
- API contracts: endpoints, inputs, outputs, status codes, error model
- Event contracts: schemas, ordering guarantees, idempotency assumptions
- Data contracts: tables or views exposed, semantics, allowed writes, retention
- UX contracts: state model (loading/error/empty), performance budgets, accessibility requirements
- Operational contracts: SLOs, rate limits, escalation paths, maintenance windows
A contract checklist you can copy into reviews
Use this to make “we have an API” become “we have a reliable interface.”
| Contract area | What to make explicit | Why it matters |
|---|---|---|
| Inputs and validation | types, required fields, constraints | prevents silent bad data and ambiguous behavior |
| Errors | stable error codes, retryability, messaging | reduces brittle client logic and incident time |
| Versioning | compatibility rules, deprecation policy | enables evolution without “flag days” |
| Performance | latency targets, pagination, limits | avoids accidental timeouts and cost blowups |
| Security | authn/authz model, scopes, tenancy rules | closes “who can call what?” gaps |
| Reliability | timeouts, idempotency keys, backoff expectations | prevents thundering herds and cascading failure |
Contracts are strongest when they are enforced
A contract that only lives in a wiki is optional. A contract that is checked in CI is real.
Common enforcement mechanisms:
- Schema validation (OpenAPI, JSON Schema, Protobuf)
- Consumer-driven contract tests (to detect breaking changes early)
- Compatibility checks (backward compatible schema evolution)
- Canary releases and telemetry-based rollout gates
If you already practice “thin vertical slices,” treat the slice as a contract proving ground: ship one end-to-end user journey, then harden the contracts you discovered along the way.
Ownership: who is accountable for outcomes
Ownership is the part most teams skip, and it is often the root cause of slow delivery and incident chaos.
Ownership answers:
- Who can approve a breaking change?
- Who gets paged when it fails?
- Who funds and prioritizes reliability and tech debt work?
- Who owns the data quality and correctness?
What “good ownership” looks like
At minimum, every meaningful system component should have:
- A named owning team (not “Engineering”)
- A documented support path (including incident escalation)
- A backlog and decision rights for changes
- A basic operational posture (dashboards, alerts, runbook)
A lightweight artifact many teams adopt is a service catalog entry (even if it starts as a markdown file in the repo). It typically captures boundary, contract, and ownership in one place.
Ownership model table (simple and usable)
| Thing | Owner’s responsibilities | “Not the owner’s job” (to prevent confusion) |
|---|---|---|
| API/service | roadmap alignment, runtime reliability, change safety, support | building every consumer feature or UI workflow |
| Data domain | schema evolution, data quality, access rules, governance | ad hoc analytics requests without prioritization |
| Platform/infrastructure | paved path, CI/CD, environments, guardrails | taking over app-specific debugging forever |
| Shared library | versioning, compatibility, security fixes | becoming a dumping ground for unrelated helpers |
Ownership is not about control, it is about predictable change.
How the three fit together (a practical loop)
Treat boundaries, contracts, and ownership as a loop you revisit whenever you add new capabilities.
- A boundary without a contract creates ambiguity.
- A contract without ownership becomes stale.
- Ownership without a clear boundary turns into endless “support everything.”
A pragmatic workflow many teams use:
- Map boundaries for one business capability (not the whole enterprise).
- Write contracts for the interfaces that cross those boundaries.
- Assign explicit owners and support expectations.
- Add enforcement (tests, CI checks, rollout gates) on the most critical contracts first.
This is also the safest way to integrate external parties. If you syndicate availability or listings to partner sites, you want a clean integration boundary and a stable contract so your core system does not get coupled to a partner’s frequent content changes.
Common failure modes (and what to do instead)
“Everything depends on everything”
Symptom: a small change triggers large test cycles, many approvals, or frequent regressions.
Fix: introduce a boundary where change cadence differs, then enforce contracts with integration tests and versioning rules.
“We have microservices, but releases are still slow”
Symptom: lots of deployables, but still tightly coupled coordination.
Fix: audit contracts and ownership. Many microservice landscapes fail because APIs are not stable, data writes are shared, and nobody owns cross-service reliability.
“No one owns the database”
Symptom: schema changes break consumers, data meaning drifts, quality issues linger.
Fix: assign data domain ownership and define which services can write which records. If you must share a database temporarily, enforce write ownership at the application layer and plan a migration.
“The UI is a coupling amplifier”
Symptom: frontend calls many backends directly, errors are inconsistent, performance is unpredictable.
Fix: define UX contracts (state model, error handling, performance budgets) and consider a BFF (backend-for-frontend) boundary when appropriate.
A fast self-assessment (15 minutes)
If you want a quick signal of maturity, answer these questions:
| Question | If the answer is “no” | What to do next |
|---|---|---|
| Can we list our main system components and their boundaries? | Hidden coupling is guaranteed | Create a one-page system map and name the seams |
| Do we have written contracts for the top 5 integrations? | Breaking changes will be frequent | Add minimal OpenAPI/schema docs and error models |
| Can every component be tied to an owning team? | Incidents and tech debt will stall | Assign ownership and define escalation paths |
| Are contracts enforced in CI for critical paths? | Docs will drift | Add contract tests and compatibility checks |
| Do owners publish SLOs or at least reliability targets? | Reliability work is unplanned | Start with one SLI and one SLO per critical service |
If you want a deeper architecture-centric checklist, Wolf-Tech also outlines what an expert typically inspects during a review: What a Tech Expert Reviews in Your Architecture.
Frequently Asked Questions
What is the difference between a boundary and a contract in software systems? A boundary defines what’s inside a component (responsibility scope). A contract defines how that component interacts with the outside world (a testable promise).
Do we need microservices to have good boundaries? No. You can enforce strong boundaries inside a monolith using modules, dependency rules, and clear data ownership. Microservices only move boundaries into runtime.
What should be in an API contract besides endpoints? At minimum: validation rules, error model (stable codes), versioning and deprecation policy, performance limits (pagination, rate limits), and security expectations.
Who should own shared libraries? A named team should own the library’s versioning, compatibility, security fixes, and deprecation policy. Without ownership, shared code quickly becomes brittle and risky to change.
How do we start if our system is already messy? Start small: pick one high-value business capability, map its boundary, define contracts at the seams, assign ownership, then add enforcement in CI. Expand from there.
Need clearer boundaries, contracts, or ownership in your system?
Wolf-Tech helps teams design and evolve software systems that are safer to change, easier to operate, and easier to scale, without betting the business on risky rewrites. If you want a second set of eyes on your architecture and delivery risks, explore Wolf-Tech at wolf-tech.io and start a conversation about an architecture review, contract hardening, or ownership model reset.

