Technology Software Strategy: What to Standardize First

Tool sprawl is easy to create and painfully hard to unwind. One team picks a CI tool “just for now,” another standardizes on a different logging stack, a third buys a SaaS workflow engine, and suddenly your technology software strategy is mostly about negotiating mismatches instead of shipping value.
Standardization is how you buy back speed and reduce production risk, but only if you standardize the right things, in the right order, and at the right level of rigidity. This guide gives you a pragmatic sequence you can apply in weeks, not quarters.
What “standardize” should mean in a modern technology software strategy
Standardization is not “one tool for everything.” It is making key decisions repeatable so teams can deliver safely without re-litigating fundamentals every sprint.
A useful definition:
- Standards are non-negotiable baselines that reduce risk (for example, how you handle secrets, how deployments are promoted, what must be logged).
- Paved roads are default paths that are easiest to use (for example, templates, reference repos, self-service environments).
- Guardrails are constraints with autonomy inside them (for example, supported databases, approved identity patterns, minimal SLOs).
If your standard forces teams into workarounds, it is not a standard, it is friction.
The core rule: standardize by risk and coordination cost first
When leaders ask “what should we standardize first,” they often start with frameworks or languages because those are visible. That is usually backward.
The best early standards have three properties:
- High risk reduction (security, downtime, data loss)
- High coordination cost if inconsistent (every team must integrate, operate, or support it)
- Hard to retrofit later (identity, logging, delivery, data contracts)
To make prioritization concrete, use this simple scoring lens.
| Standardization candidate | Risk reduced | Coordination cost reduced | Retrofit cost if delayed | Typical owner |
|---|---|---|---|---|
| Identity and access patterns | High | High | High | Platform/security + app leads |
| CI/CD and environment promotion | High | High | Medium to High | Platform/DevOps |
| Observability and incident workflow | High | Medium to High | High | SRE/operations |
| Data and integration contracts | Medium to High | High | High | Architecture + domain teams |
| Secure SDLC baseline (SCA, secrets, SBOM) | High | Medium | Medium | Security + platform |
| “Reference stack” for new services | Medium | Medium | Medium | Architecture guild |
| UI component library/design system | Low to Medium | Medium | Medium | Frontend platform/design |
| Language or framework mandate | Variable | Low | Medium | Architecture leadership |
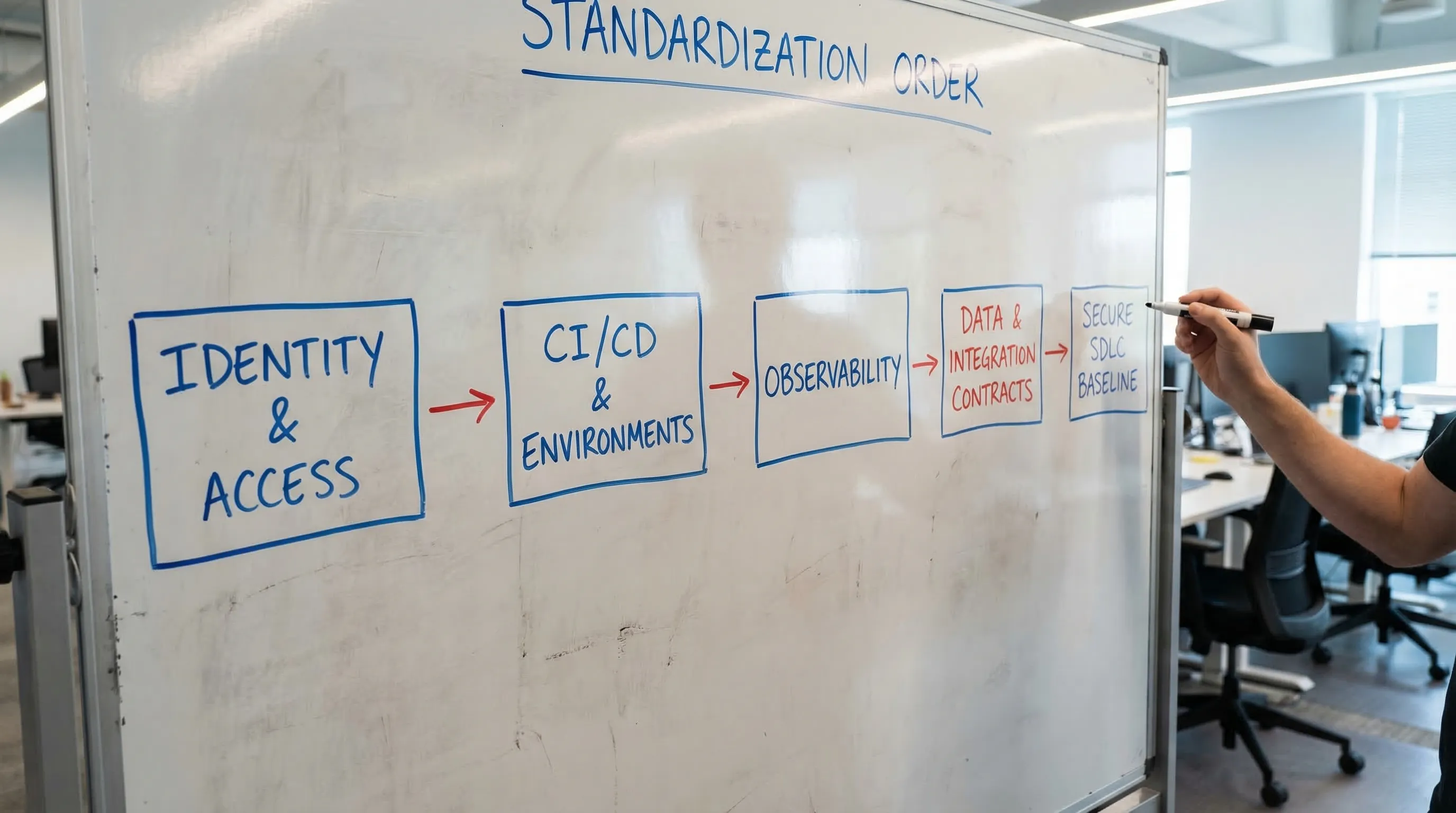
The sequence below follows this lens.
What to standardize first (a practical sequence)
1) Identity, authorization, and service-to-service trust
If you standardize nothing else, standardize who can do what, and how services prove it.
Why this comes first:
- Auth patterns are cross-cutting and expensive to rewrite.
- Inconsistent authorization leads to the worst kind of incidents (quiet data exposure).
What “good” looks like as a standard:
- One primary identity provider pattern (OIDC/OAuth2), with clear guidance for web apps, mobile, and machine clients.
- A documented authorization approach (RBAC/ABAC decisions, where checks live, how they are tested).
- A service-to-service trust baseline (mTLS where required, workload identity where available, no long-lived static credentials).
Deliverable you can ask for: a one-page auth blueprint plus a reference implementation repo.
2) CI/CD, release promotion, and environment strategy
You are not standardizing “a pipeline tool.” You are standardizing how change moves to production.
A minimal, high-leverage baseline includes:
- A shared branching and promotion model (trunk-based or clearly defined alternatives)
- Automated deploys to a non-prod environment per change (preview environments where feasible)
- Promotion rules (who can promote, what tests are required, how rollbacks work)
- Artifact versioning and provenance (so you know what was deployed)
If you want a metric-backed way to measure improvement, Google Cloud’s DORA research is a widely used benchmark for delivery performance and stability (Accelerate/DORA metrics overview).
3) Observability standards (logs, metrics, traces) plus incident basics
Most teams try to “add monitoring” after the first outage. Standardize it early so every service is diagnosable by default.
Standardize:
- Structured logging conventions (correlation IDs, tenant/user identifiers where appropriate, PII redaction rules)
- Service health signals (the few golden signals you always expose)
- Tracing propagation rules across HTTP and async boundaries
- Alert hygiene (alert on symptoms tied to user impact, not raw resource graphs)
- An incident workflow (severity levels, comms channel, post-incident review template)
Deliverable you can ask for: a “definition of done” that includes an observability checklist.
4) Data and integration contracts (the hidden tax in most portfolios)
If your systems are a network, contracts are the roads. Without standards, every integration becomes custom infrastructure.
Prioritize standardizing:
- API styles that your org supports (REST, GraphQL in specific cases, event-driven patterns)
- Versioning rules and deprecation policy
- Schema management (OpenAPI/AsyncAPI, JSON schema, protobuf, whichever fits)
- Contract testing expectations for critical dependencies
- Canonical identifiers (customer ID, account ID) and where they are sourced
This is also where you prevent “integration drift,” where teams start depending on undocumented fields or side effects.
If you want a deeper systems view, Wolf-Tech’s guide on boundaries and contracts is a good companion reading: Software Systems 101: Boundaries, Contracts, and Ownership.
5) Secure SDLC baseline (supply chain, secrets, dependencies)
Security standards work best when they are boring and automated.
A pragmatic baseline:
- Dependency scanning (SCA) and vulnerability triage SLA
- Secrets scanning and secrets management rules
- Minimal SBOM expectations for deployable artifacts
- Container/image hardening guidelines where relevant
- A policy for AI-assisted coding and licensing/IP handling (if you use it)
If you need an authoritative reference point, the NIST Secure Software Development Framework (SSDF) is a solid starting map.
6) A reference stack for “new things,” not a forced rewrite mandate
After the cross-cutting foundations are in place, define a reference stack that makes new work cheaper.
Key point: standardize the default, not every existing system.
A good reference stack package includes:
- One or two approved service templates (API service, background worker)
- Standard libraries for auth, logging/tracing, configuration, and error handling
- A default data store choice per use case (for example, relational by default unless proven otherwise)
- Operational runbooks and SLO starter targets
This is where you reduce decision fatigue without freezing innovation.
To avoid repeating old mistakes, validate stacks with thin vertical slices (a small end-to-end feature shipped safely). Wolf-Tech covers this evaluation mindset in: Apps Technologies: Choosing the Right Stack for Your Use Case.
What not to standardize first (common traps)
Standardization can backfire when it is used to create certainty instead of reducing real risk.
Don’t start with “one language, one framework”
Language mandates are easy to announce and hard to justify economically. You often end up paying for rewrites, talent churn, and mismatched tools.
Standardize outcomes and interfaces first (delivery, contracts, security). Let teams earn exceptions with evidence.
Don’t build an internal platform before you have platform behaviors
A platform is not a Kubernetes cluster. It is a product with users (engineers), feedback loops, and support.
If you do not yet have:
- clear ownership
- a roadmap
- adoption metrics
- support and docs
Then start with templates and guardrails, not a big platform rebuild.
Don’t “standardize” by procurement spreadsheet
Many orgs standardize software by selecting vendors centrally, then discover teams bypass the decision because it does not fit workflows.
A better model is to standardize:
- the integration pattern
- data export/portability expectations
- security requirements
Then choose tools that comply.
A lightweight 30-day plan to standardize the right first layer
If you need momentum, treat standardization like delivery: ship a small, usable baseline.
Week 1: Inventory and pick the top 3 standards
Create a short map:
- What are your top 10 services/systems?
- How do they authenticate?
- How do they deploy?
- Can you trace a user request end-to-end?
- What are the top recurring incidents?
Pick three standards that directly reduce your biggest risks.
Week 2: Write standards as “developer behaviors”
Avoid policy documents that no one reads. Write:
- a one-page standard
- a reference implementation
- CI checks that enforce the non-negotiables
Week 3: Pilot with one real team and one real change
Apply the standards to a real slice (new endpoint, new job, new UI flow). Fix friction and missing docs.
Week 4: Roll out with opt-in defaults, then lock in the baseline
Make the paved road easiest. When adoption is working, make the risk-related parts mandatory (for example, secrets scanning, correlation IDs).
A quick example: standardization is not just for “tech companies”
Even small service businesses run on software workflows: lead capture, scheduling, payments, content publishing, file storage, and analytics.
Even a creative studio or destination-event business benefits from the same first principles: standardize identity and access to customer data, standardize how files are stored and shared, and standardize the “handoff” between marketing, booking, and production so operations do not depend on tribal knowledge.
The tools will differ from a SaaS company, but the strategy is identical: reduce risk and coordination cost first.
Frequently Asked Questions
What is the difference between standardization and centralization? Standardization defines shared rules and defaults (guardrails and paved roads). Centralization moves control to one team. You can standardize without centralizing by using templates, automation, and clear exception paths.
How do we enforce standards without slowing teams down? Automate enforcement in CI/CD (linting, security checks, policy as code) and provide reference implementations. If engineers have to “ask permission” for basics, your standard is too manual.
Should we standardize cloud providers first? Usually no. Standardize delivery, identity, observability, and contracts first. Cloud decisions become easier when you can measure reliability, performance, and cost consistently.
When does a reference stack become harmful? When it turns into a mandate that blocks valid use cases, or when it is not maintained. A reference stack should be a default with an upgrade path and visible ownership.
How do we handle legacy systems while standardizing? Standardize what touches them first (identity gateways, logging, deployment safety, integration contracts). Avoid big rewrites. Incrementally add seams that let you improve safety without stopping delivery.
Make standardization executable with Wolf-Tech
If you are trying to turn a technology software strategy into something teams can actually follow, Wolf-Tech can help you design and implement pragmatic standards across full-stack delivery, code quality, legacy optimization, cloud and DevOps, and integration patterns.
A good starting point is a short assessment that produces: a prioritized standardization backlog, reference templates, and a rollout plan tied to measurable delivery and reliability outcomes. Learn more about Wolf-Tech’s approach at wolf-tech.io.

