Software Implementation Plan: Cut Risk With Milestones

A software implementation plan is where good intentions become production reality. Most implementation risk is not “coding risk”, it is uncertainty about integrations, data, security, operability, and user adoption. The fastest way to cut that risk is to structure the work around milestones that produce proof, each with clear exit criteria, not around a long feature list.
This guide gives you a milestone-based software implementation plan you can reuse for custom builds, legacy modernization, or rolling out a packaged platform with significant integration and data migration work.
What a software implementation plan is (and what it is not)
A useful software implementation plan does three jobs:
- Aligns outcomes and constraints so teams build the right thing under real-world limits (time, budget, compliance, uptime).
- Reduces uncertainty early by forcing proof on the riskiest assumptions first.
- Creates a safe path to production with repeatable delivery, measurable reliability, and reversible releases.
What it is not: a Gantt chart that pretends everything is known up front.
If you want a deeper kickoff structure that feeds into this plan, pair this article with Wolf-Tech’s guide on software project kickoff: scope, risks, and success metrics.
Step 1: Define success in three layers (business, delivery, production)
Before you define milestones, define what “done” means in a measurable way. A practical implementation plan tracks three layers of success:
Business outcomes (why ship)
Examples (choose 1–3): reduce processing time, improve conversion, cut support volume, unlock a new market, meet compliance deadlines.
Delivery health (can we ship predictably)
Use a small set of flow and stability metrics. Many teams start with the four DORA metrics (deploy frequency, lead time, change failure rate, time to restore). The annual DORA research is a useful reference point.
Production outcomes (will it behave in the real world)
Define a few non-functional targets that matter to users and operations, such as p95 latency, availability, error rate, and incident response expectations.
A simple rule: if you cannot measure it, you cannot manage it during implementation.
Step 2: Use milestones as “risk proof gates”
Milestones work when each one burns down a named risk and produces artifacts you can validate (demos, tests, dashboards, runbooks), not just documents.
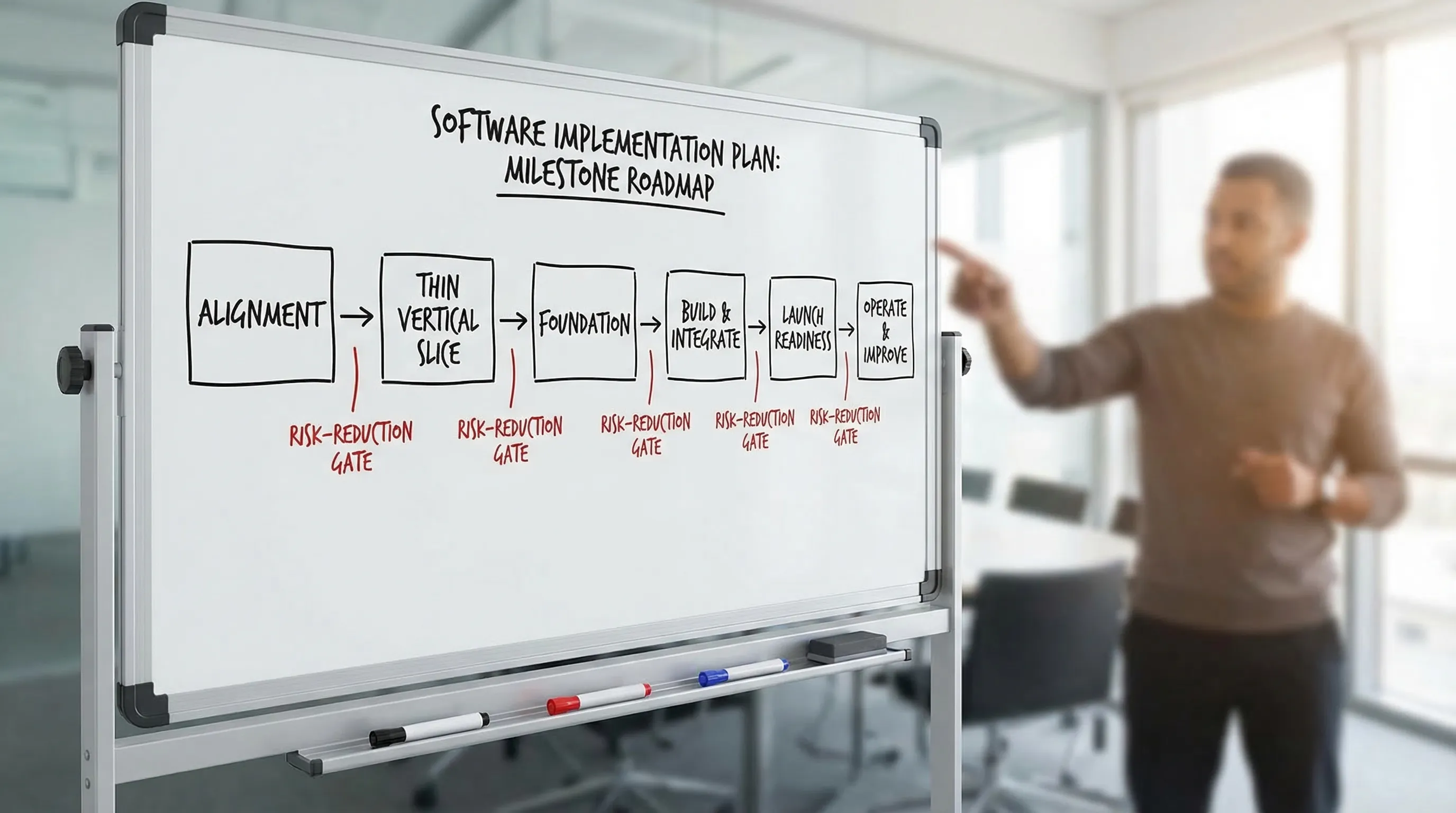
A milestone-based software implementation plan (template)
The milestone model below is intentionally generic so you can adapt it to your context (new product, modernization, ERP/CRM rollout, internal platform rebuild).
| Milestone | Goal (risk reduced) | Typical proof (exit criteria examples) | Core artifacts |
|---|---|---|---|
| 1) Alignment and scope boundaries | Prevent “building the wrong thing” | One-page scope with explicit out-of-scope, named top risks with owners, success metrics agreed | Scope brief, risk register, decision-rights map, Definition of Done |
| 2) Thin vertical slice | Prove feasibility end-to-end | A production-like slice works through UI, API, data, auth, and one critical integration | Slice demo, API contracts, data model draft, deployment path validated |
| 3) Foundation (delivery + architecture baseline) | Prevent slow, unsafe delivery later | CI/CD runs on every change, basic test strategy, environments and secrets flow, observability baseline | Architecture baseline, pipeline, quality gates, telemetry standards |
| 4) Build and integrate (incremental releases) | Control scope and integration surprises | Regular production-like demos, contract tests, migration rehearsals, progressive rollout ready | Iteration plan, integration contracts, migration scripts, feature flags |
| 5) Launch readiness and cutover | Make launch reversible | Go-live checklist complete, rollback plan tested, SLOs and on-call expectations defined | Runbooks, dashboards, incident playbook, cutover plan |
| 6) Operate and improve | Avoid “launch and forget” | Post-launch metrics reviewed, reliability issues triaged, backlog re-prioritized by real usage | Post-launch review, SLO tracking, improvement roadmap |
If your program includes significant UX work, bake in a milestone deliverable that aligns UX and engineering early. Wolf-Tech calls this the “handshake” between UX decisions and system contracts: UX to architecture handshake.
Step 3: Define exit criteria that are hard to fake
Exit criteria should be verifiable by someone other than the implementers. A practical pattern is to require at least one item in each category:
- Product proof: a demo in a production-like environment using realistic data.
- Engineering proof: tests, quality gates, and review rules that run automatically.
- Operational proof: logs/metrics/traces and a dashboard that answers, “Is it healthy?”
- Security proof: threat model notes or baseline controls, plus dependency and secret scanning.
This keeps milestones from becoming status theater.
Step 4: Attack the highest-risk work earlier than feels comfortable
Most implementation plans fail because teams defer the hard parts. Milestones let you pull risk forward deliberately.
High-risk area: integrations
Integrations create hidden complexity: rate limits, idempotency, retries, and contract drift.
Milestone tactic:
- In Milestone 2, integrate at least one real external dependency (payments, identity, CRM, data warehouse) end-to-end.
- Add contract tests in Milestone 3 or early Milestone 4 so you detect breaking changes before production.
High-risk area: data migration
Data migration risk is not only volume, it is correctness, backfills, and cutover consistency.
Milestone tactic:
- Make migration a first-class backlog item, not “release week work.”
- Rehearse migrations in Milestone 4 with production-shaped data, including timing and rollback.
If you are modernizing legacy systems, plan for incremental replacement patterns and reversible change. A practical reference is the Strangler approach discussed in many modernization playbooks (Wolf-Tech also covers modernization strategies in modernizing legacy systems without disrupting business).
High-risk area: security and compliance
Security is easiest when treated as defaults and automated checks.
Milestone tactic:
- Establish baseline controls early (Milestone 3): dependency scanning, secret scanning, least-privilege access, audit logging expectations.
- If you need a recognized framework as a starting point, see the NIST Secure Software Development Framework (SSDF).
High-risk area: performance and reliability
Performance and reliability regressions often appear late because teams measure too late.
Milestone tactic:
- Define performance budgets and SLO targets in Milestone 1.
- Instrument the thin slice in Milestone 2 so you can see latency and errors before the app is “complete.”
For reliability-specific practices (timeouts, retries, safe deploys), Wolf-Tech’s backend reliability best practices is a useful complement.
High-risk area: adoption and change management
The best implementation still fails if users do not switch.
Milestone tactic:
- Add an enablement track starting in Milestone 1: training, comms, permission mapping, and support model.
- In Milestone 4, run a pilot cohort behind feature flags and measure actual workflow completion.
Step 5: Put governance on rails (decisions, cadence, ownership)
Milestones reduce risk only if people can make decisions quickly and consistently.
Decision rights (who can decide what)
A lightweight decision-rights map prevents escalations and surprises.
| Decision type | Typical owner | When to decide | Evidence required |
|---|---|---|---|
| Scope boundary changes | Product owner + sponsor | Before sprint planning | Impact on timeline, cost, and risk register |
| Architecture baseline and constraints | Tech lead/architect | By end of Milestone 3 | Thin slice findings, operability needs |
| Go-live criteria | Sponsor + engineering + operations | During Milestone 5 | Checklist completion, rollback proof, SLO readiness |
| Data migration cutover approach | Engineering + data owner | Early Milestone 4 | Rehearsal results, reconciliation plan |
Cadence that matches milestones
Keep it simple:
- Weekly milestone review: risks burned down, proofs achieved, next risk focus.
- Biweekly demo: working software, not slides.
- Change review: a short ritual to keep releases safe (especially in Milestone 4 and 5).
If your org struggles to turn agile rituals into shipped outcomes, Wolf-Tech’s agile development that ships provides a practical operating model.
An example timeline (adaptable) for an 8–12 week implementation cycle
Timelines vary, but many teams benefit from a short, intense plan that forces early proofs. Here is a common shape:
| Weeks | Primary milestone focus | What you should be able to show |
|---|---|---|
| 1–2 | Alignment and thin slice planning | Scope boundaries, risk register, slice definition, success metrics |
| 3–4 | Thin vertical slice | End-to-end slice demo in a production-like environment |
| 5–6 | Foundation | CI/CD, quality gates, environments, observability baseline |
| 7–10 | Build and integrate | Incremental releases, integration proofs, migration rehearsals |
| 11–12 | Launch readiness | Cutover rehearsal, rollback tested, runbooks and dashboards |
The key is not the exact week count. The key is not advancing without proof.
Copyable checklist: milestone exit criteria (starter set)
Use this to pressure-test your plan. If many items are “TBD,” your milestones are not yet doing their job.
Milestone 2 (thin vertical slice) exit criteria
- One core user journey works end-to-end (UI, API, data, auth).
- At least one real integration is exercised (or a contract-faithful sandbox).
- Basic telemetry exists: request logs, error tracking, and a simple health dashboard.
- A rollback path exists for the slice deployment.
Milestone 5 (launch readiness) exit criteria
- Go-live checklist reviewed with engineering, ops, and business stakeholders.
- Rollback procedure rehearsed (not only written).
- Data migration cutover rehearsed with reconciliation checks.
- On-call expectations defined, runbooks available, incident channel ready.

Common failure modes (and the milestone fix)
Failure mode: “We will integrate later.” Fix: Make an integration part of the thin slice.
Failure mode: “We will handle performance after MVP.” Fix: Instrument the slice and set a basic budget early.
Failure mode: “CI/CD is nice to have.” Fix: Treat delivery as a product capability in Milestone 3.
Failure mode: “Launch is a date.” Fix: Treat launch as a reversible risk event in Milestone 5.
Frequently Asked Questions
What is included in a software implementation plan? A good software implementation plan includes outcomes and success metrics, milestone gates with exit criteria, a risk register, delivery and quality practices (CI/CD, tests), integration and data migration plans, and launch readiness artifacts (runbooks, rollback, monitoring).
How do milestones reduce software implementation risk? Milestones reduce risk by forcing early proof of the hardest assumptions (integrations, data migration, performance, security) and by preventing the team from progressing without verifiable exit criteria.
What is a thin vertical slice in software implementation? A thin vertical slice is a small, end-to-end implementation of one real user journey across UI, backend, data, and infrastructure, built in a production-like way to prove feasibility and expose hidden work early.
How do you define go-live criteria for implementation? Define go-live criteria as a checklist of verifiable proofs: monitored service health, rehearsed rollback, rehearsed data cutover, operational ownership, and SLO readiness. Avoid criteria that are purely subjective, like “it looks stable.”
How long should a software implementation plan be? The plan should be as long as needed to remove ambiguity, but no longer. Many teams succeed with a 1–3 page plan plus linked artifacts (risk register, milestone checklists, and architectural notes).
Want a milestone plan tailored to your system and risks?
If you are implementing custom software, modernizing a legacy application, or rolling out a platform that depends on real integrations and data migration, Wolf-Tech can help you turn milestones into proof gates with practical delivery, code quality, and cloud and DevOps expertise.
Start with a quick conversation at Wolf-Tech and bring whatever you already have (scope notes, architecture sketches, vendor proposals, or a backlog). We will help you pressure-test the plan, identify the riskiest assumptions, and define milestones that cut risk early instead of discovering it at go-live.

