Software Industries: What Changes Across Domains

Most software failures are not caused by “bad code.” They happen when a product team builds the right thing for the wrong domain: the wrong compliance assumptions, the wrong data lifecycle, the wrong integration model, or the wrong definition of “reliable.”
Across software industries, your fundamentals stay the same (clear requirements, sound architecture, quality gates, observability), but the constraints that shape those fundamentals change dramatically.
This article breaks down what actually changes across domains, and how to adapt your architecture, delivery plan, and build-vs-buy decisions without overcomplicating your stack.
What actually changes across software industries
Industry differences are not “just requirements.” They reshape your system’s boundaries, risk model, and operating expectations.
1) The risk profile (and who pays for mistakes)
In some domains, a bug is a support ticket. In others, it is an audit finding, a chargeback wave, a privacy incident, or a safety issue.
A practical rule: risk determines rigor. Higher risk demands stronger proofs (testing depth, change controls, access controls, incident readiness), not “more process for its own sake.”
2) Regulations, audits, and evidence
Regulated industries do not only require secure behavior, they require provable security.
That changes what “done” means:
- You need traceability from requirements to implementation to tests.
- You need security controls you can demonstrate (not just promise).
- You need logs and retention policies aligned with legal and contractual needs.
If you want a broadly applicable reference point for secure development practices, the NIST Secure Software Development Framework (SSDF) is a useful baseline.
3) Domain workflows and data semantics
Two apps can look identical on the surface (search, forms, approvals) but behave differently because the domain rules differ:
- Finance: money movement, ledgers, reconciliation.
- Healthcare: clinical documentation, consent, PHI.
- Education: rostering, courses, assignments, accessibility.
- Real estate: listings, availability, lead routing, document flows.
When teams skip explicit domain modeling, they often rebuild the same flows repeatedly and accumulate “invisible complexity” in the UI.
4) Integration landscape and “system of record” ownership
Some industries are integration-first:
- Payments, fraud, KYC, credit bureaus.
- EHR/EMR and lab systems.
- LMS/SIS and identity providers.
- MLS feeds, map providers, signing and payment.
The hardest problems are frequently at boundaries. Treat API and data contracts as first-class artifacts. (Wolf-Tech’s view on this is consistent across domains: clear boundaries, explicit contracts, and named ownership are what make systems predictable. See Software Systems 101: Boundaries, Contracts, and Ownership.)
5) Non-functional requirements (NFRs) that are not negotiable
Performance, reliability, and security targets are not generic “best practices.” They are domain-dependent constraints.
- Real-time bidding, trading, and fraud checks push latency expectations.
- Clinical workflows demand continuity and privacy.
- Education peaks create seasonal load spikes.
- E-commerce demands conversion-safe performance and experimentation.
6) Procurement, rollout, and change management
A B2B enterprise rollout looks nothing like a self-serve consumer launch.
What changes:
- Sales cycle and stakeholder count.
- Security questionnaires and vendor risk.
- Data migration and integration sequencing.
- Release governance and approval workflows.
If you sell into enterprise or regulated buyers, “shipping” must include operability and evidence, not just feature completion.
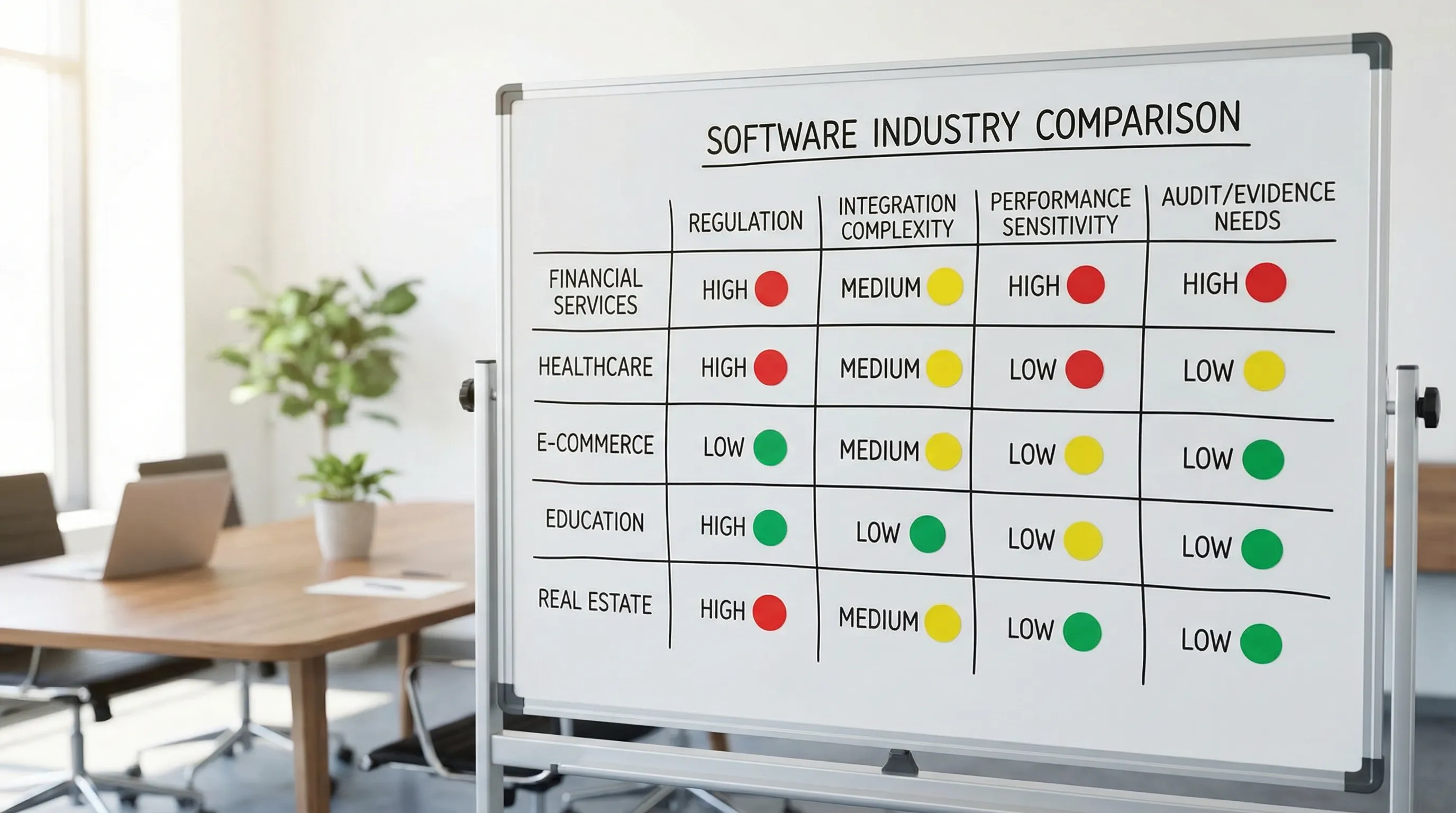
A quick cross-domain comparison table
Use this as a starting lens when you evaluate a new industry or expand into one.
| Domain | What drives complexity | Integration reality | “Proof” you need early | Common pitfall |
|---|---|---|---|---|
| Financial services | Risk, fraud, correctness, auditability | Many third parties (payments, identity, reporting) | Transaction correctness, idempotency, audit trails | Treating money flows like normal CRUD |
| Healthcare | Privacy, consent, clinical workflows | EHR/EMR, scheduling, claims, identity | Access control, data minimization, logging, retention | Bolting security on after UX is done |
| E-commerce / retail | Conversion, catalog/search, experimentation | Payments, inventory, shipping, marketplaces | Core Web Vitals, resilience to third-party outages | Performance treated as a late optimization |
| Education | Multi-role UX, accessibility, seasonal scale | LMS/SIS, SSO, content providers | Role model, permissions, accessibility, data governance | Underestimating admin and reporting needs |
| Real estate | Marketplace dynamics, messaging, document flows | MLS, maps, payment, signing, CRM | Data freshness, ingestion reliability, permissions | Letting integrations dictate your core model |
Domain deep dives: what to change (and what to keep)
Below are practical, high-signal shifts by industry. The goal is not to prescribe one “correct architecture,” but to highlight what your system must respect.
Financial services software: correctness and auditability first
What changes:
- Data models often need ledger-like properties (immutable records, traceability, reconciliation).
- Stronger constraints around access, fraud prevention, and operational resilience.
- Heavier vendor due diligence (SOC 2, penetration tests, security questionnaires).
Architecture and delivery implications:
- Prefer explicit transaction boundaries and idempotent APIs.
- Design for failure: timeouts, retries, and clear compensation logic.
- Treat audit logs as product features, not infrastructure noise.
Wolf-Tech’s deeper take on this domain is covered in Software Development for Financial Services: What to Know.
Healthcare software: privacy, consent, and workflow realism
What changes:
- Handling sensitive health data (PHI) increases security and privacy expectations.
- Consent, access control, and “minimum necessary” access become central design constraints.
- The UX must match real clinical and administrative workflows, including exceptions.
A concrete example of what “workflow realism” means: a mental health practice might need scheduling, secure intake, telehealth coordination, and documentation that fits clinical routines. If you are building for this space, reviewing how real providers describe their services can be useful context, for example this page on comprehensive psychiatric services in NYC.
Architecture and delivery implications:
- Build security into your baseline (threat modeling, least privilege, secure defaults). OWASP’s ASVS is a practical checklist-style reference.
- Make data lifecycle explicit: retention, deletion, exports, and access auditing.
- Expect integration and interoperability needs (often uneven maturity across vendors).
E-commerce and retail: performance equals revenue
What changes:
- Performance directly impacts conversion, SEO, and paid acquisition efficiency.
- Experimentation (A/B tests), personalization, and marketing tooling introduce third-party risk.
- Inventory and fulfillment create complex state transitions and edge cases.
Architecture and delivery implications:
- Put performance budgets and monitoring in place early, not after growth.
- Isolate third-party scripts, fail gracefully, and design for partial outages.
- Build strong observability around checkout and critical funnels.
If your front end is React-based, Wolf-Tech’s React Website Performance: Fix LCP, CLS, and TTFB is a practical companion.
Education software: roles, accessibility, and institutional constraints
What changes:
- Many roles: students, educators, admins, guardians, IT.
- Accessibility is not optional in many contexts, it is part of usability and procurement.
- Integrations with SIS/LMS and rostering drive data complexity.
Architecture and delivery implications:
- Treat identity and authorization as core domain features.
- Invest in admin tooling, reporting, and data governance early.
- Plan for seasonal load (back-to-school spikes) and support workflows.
Wolf-Tech covers common platform needs in Education Software Development: Must-Have Features.
Real estate software: data freshness and marketplace mechanics
What changes:
- Data is often ingested from external sources (listings, availability, agent info).
- Freshness matters, stale data kills trust.
- Messaging, scheduling, and document flows introduce multi-party state.
Architecture and delivery implications:
- Design ingestion pipelines with observability (what changed, when, why).
- Make permissions and visibility rules explicit (brokerage, agent, tenant, owner roles).
- Separate “core model” from “feed model” to avoid vendor-driven domain design.
A practical checklist: adapt your plan when you enter a new domain
When teams move across software industries, they often reuse a tech stack but forget to reuse a decision process. This lightweight set of artifacts is usually enough to avoid expensive misalignment.
Create a one-page domain context pack
Include:
- Primary users and critical workflows (including failure states)
- Data types, sensitivity, and retention needs
- Key integrations and system-of-record assumptions
- NFR targets (security, reliability, latency, scale)
- Compliance expectations (what you must prove, not just implement)
Validate with a thin vertical slice
A thin slice should cross the real seams: UI, API, data, identity, an integration, and deployment. It should produce evidence.
| Proof area | What “good” looks like in week 2 to 4 |
|---|---|
| Security baseline | Auth in place, least privilege, secrets handled correctly, basic abuse protections |
| Reliability | Timeouts/retries defined, error handling paths tested, rollback plan exists |
| Data correctness | Domain rules enforced, migration strategy considered, audit trail approach sketched |
| Operability | Logs, metrics, traces for critical flows, alerting assumptions documented |
| Integration reality | One real external integration validated end-to-end |
If you need help structuring this kind of validation, Wolf-Tech’s approach is consistent across projects: de-risk early with measurable proofs (see Software Implementation Plan: Cut Risk With Milestones).
Decide build vs buy per capability, not per product
Different domains push you toward buying certain components (payments, identity, video, signing) because the compliance and reliability burden is high.
A good decision is rarely “build everything” or “buy everything.” It is typically a hybrid where you:
- Buy commoditized, high-risk infrastructure capabilities.
- Build differentiating domain workflows.
- Integrate with strict contracts and clear ownership.
Wolf-Tech outlines a practical framework in Custom Software Applications: Build vs Buy vs Hybrid.
Common mistakes when teams underestimate domain differences
Reusing architecture patterns without revalidating constraints
“Microservices worked at my last company” is not a domain argument. Your architecture should match your next 12 to 36 months of risk, team size, and operational maturity.
Treating compliance as paperwork
Compliance is an engineering reality because it changes how you store data, control access, log actions, and prove behavior.
Building the UI before the contracts
Across domains, the fastest way to prevent rework is to align UX and architecture early. If you want a deeper process for doing that, Wolf-Tech’s UX to Architecture Handshake is designed for exactly this failure mode.
Shipping without operability
In higher-risk industries, lack of observability is not a minor inconvenience. It blocks incident response, audits, and customer trust.

Frequently Asked Questions
Do software industries require completely different tech stacks? Not usually. What changes more is your security baseline, data model, integration strategy, and evidence requirements. Many stacks can work if you validate them against domain constraints.
What is the biggest difference between regulated and non-regulated domains? The need for provable controls. You must implement security, privacy, and reliability measures in ways you can demonstrate through logs, tests, documentation, and operational practices.
How do I scope an MVP for a new domain without missing critical requirements? Define an MVP as a thin end-to-end slice that proves value, usability, feasibility, and operability. Include at least one real integration and real identity/authorization in the slice.
Which domains are most integration-heavy? Financial services, healthcare, and real estate frequently have complex third-party ecosystems. The main risk is unclear system-of-record ownership and unstable contracts.
How can I avoid overbuilding when entering a new industry? Write a one-page context pack, pick the riskiest assumptions, then validate them with a short thin-slice build. Decide build vs buy per capability, and document the decision.
Need a domain-aware architecture and delivery plan?
Wolf-Tech helps teams build, optimize, and scale software across industries, with a focus on full-stack execution, code quality, legacy optimization, and pragmatic tech stack strategy.
If you are entering a new domain (or expanding into one) and want to avoid costly rewrites, consider a short architecture and delivery review to align constraints, integrations, NFRs, and proof gates before you commit to a long build.
Learn more at Wolf-Tech.

